DDoS stands for Distributed Denial of Service. This is a cyber-attack in which the attacker floods the victim’s servers with unwanted traffic by using the different systems across the internet, resulting in the crashing of the victim’s servers. This directly affects the availability of services. I am listing some tools which can be used for. Code Issues Pull requests. DDos Ripper a Distributable Denied-of-Service (DDOS) attack server that cuts off targets or surrounding infrastructure in a flood of Internet traffic. Security protection ddos ddos-attacks sql-injection web-security denial-of-service hacking-tool linux-tools ddos-tool ddos-protection attack-defense ddos. Slowloris is a tool used for DDoS attacks. It is different from other tools, as it sends legitimate HTTP traffic. This tool will not flood the victim server. It just makes a full TCP connection and requires only a few hundred requests at long-term and regular intervals. PentagonCrew DDoS Tool ## YOU NEED PYTHON 2.7 TO RUN THE SCRIPT ## Brought to you by: asund3r.
The leading, best DDoS attack tools list for every business.
Did you know that DDoS or Distributed Denial of Service is one of the most powerful tools used by the hackers? Here are few facts:
- The average cost of a DDoS attack is between $20,000-$40,000 per hour.
- The longest attack lasted for 329 hours.
- DDoS attacks are anticipated to double to 14.5 million by 2022.
Sound scary?
There is not doubt that DDoS attacks can create huge issues for companies. Just one hour of such an attack can make the customers suspect your business. The press picks up on such stories pretty early too. A best DDoS attack tool can help you prepare and stop such unfortunate circumstances.
What is a DDoS Attack?
Let’s start with the most obvious of questions. What really is a Distributed Denial of Service Attack? And why do you need to stop it?
It is an attack to make your site or other web resource unavailable through spam traffic. Imagine you have a shop and only 100 people can come in at a time. DDoS attack would be an act of sending 1000 robots in your store that are never gonna but anything. These robots will form a line and stop real users from getting in. Even if you build a better, bigger store they will increase the number of robots. The real shoppers will run away or even if they want to access their store, robots will block them.
Best DDoS Attack Tools
1. LOIC (Low Orbit Ion Cannon)
LOIC (Low Orbit Ion Cannon) is one of the best and free DDoS attack tools. This open-source is used for network testing. It was interestingly the most used tool in 2019 and 2020 to attack actual sites and cause damage. Over the last few months, LOIC (Low Orbit Ion Canon) makers have put strict protocols to stop abuse.
Ddos Tool Pastebin
Written in C#, this tool is currently hosted across the internet and available for download. You can get it from Source Forge. The open-source project keeps rolling patches and updates that you might be interested in.
You can simple open the application after installation. Then, enter the URL or IP to attack along with specifications of TCP, UDP or HTTP flood. Within seconds, this tool will send message strings and packets to select ports on the target. On the HTTP attack, however, it sends GET requests repeatedly.
2. Mister Scanner
Mister Scanner is one of the most popular vulnerability scanners. We also offer DDoS testing along with vulnerability scanning to ensure that you truly test the efficiency of your product or service.
This best DDoS attack tool sends volumetric requests after vulnerability scanning. You can even plan the attacks to ensure that business is not affected either by the scan or DDoS testing. Mister Scanner can be used to launch both Layer 7 and Layer 3 attacks. Simply enter your URL or IP, type in the select time of attack.
3. SolarWinds Security Event Manager (SEM)
When it comes to the most popular attack tools for DDoS, SEM is a powerful choice. It is a testing and mitigation tool used by some of the leading companies in the world. With proper configuration, you will be able to monitor, test, and defend against the most powerful DDoS or Distributed Denial of Services attacks in the world.
- Attack scheduling
- Configure attack types and modes
- Allows logging
- Customize filters based on specific accounts/IPs, timeframes, or combinations of filters
However, it is a costly choice for small businesses who do not need standalone tools for DDoS attack.
4. XOIC
XOIC is essentially an alternative to LOIC. It was originally built as a copy of LOIC but today it is equally popular. It is best for Layer 3, network attacks. The easy-to-use user interface makes launching attacks simple.
You simply have to enter the IP, port and protocol to launch the attack. The developers of XOIC say that it is more powerful than LOIC but we have not found that to be true. Nevertheless, XOIC DDoS attack tool is efficient with TCP/HTTP/UDP/ICMP Message to test your systems.
5. HULK (HTTP Unbearable Load King)
Need guaranteed unique requests for your DDoS attack tools? HULK (HTTP Unbearable Load King) is exactly what you need to launch such attacks. The developers of this tool have ensured that their launched attacks get past the detection systems and hurt the system.
This attack tool can launch high volume attacks that can bring down most machines. Since it is free, many attackers have also used it in the past.

- Bypasses cache engine
- Generates unique traffic an request that cannot be detected easily
- High volume traffic within seconds
You can test servers and apps with HULK and ensure that they withstand even the most powerful distributed denial of service attacks.

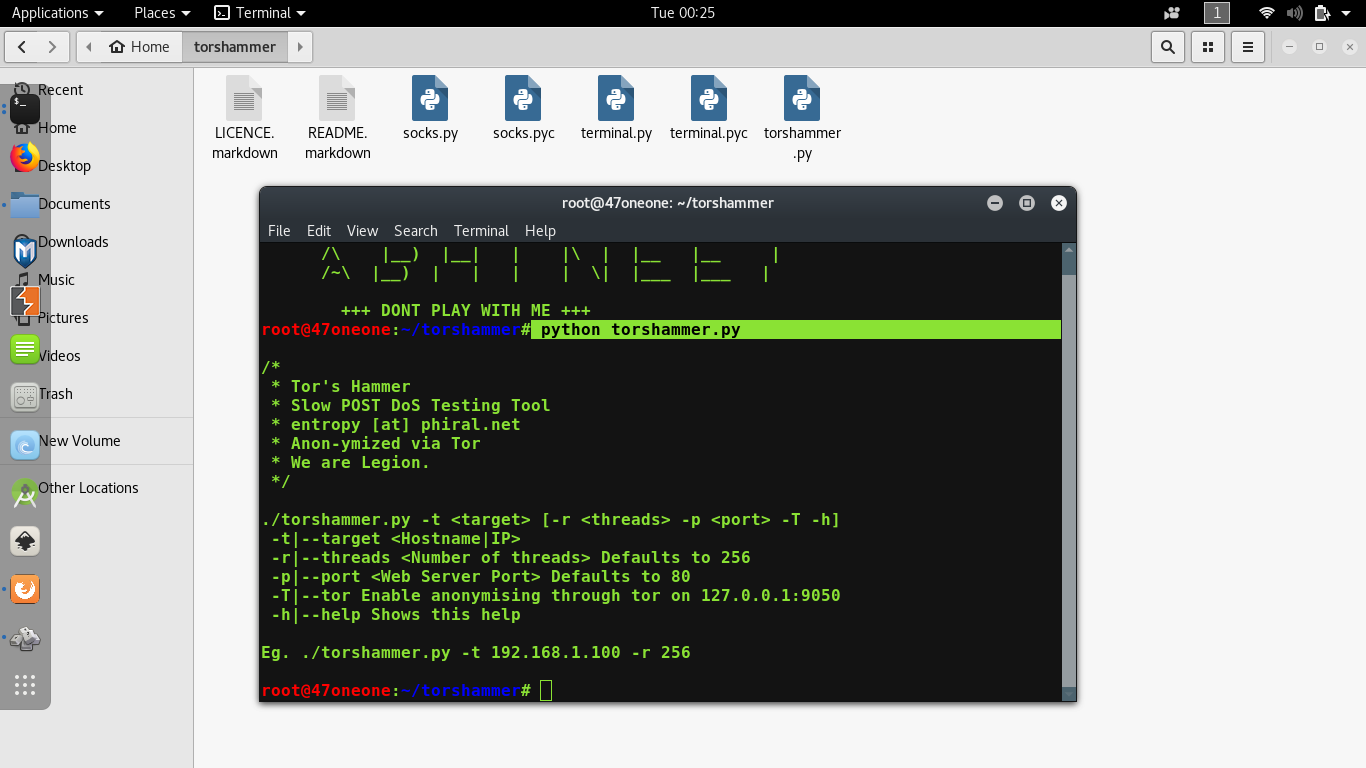
6. Tor’s Hammer
Written in Python, Tor’s Hammer is a slow post dos testing tool. This DDoS attack tool is currently in Beta but can help you push some really powerful attacks on any system. It claims to bring down any servers on Apache and IIS by a single instance. It can also run attacks through the Tor network if you have that in the system.
However, the user interface is not sleek. The user should have some knowledge of this testing tool to launch attacks efficiently.
7. DDOSIM—Layer 7 DDOS Simulator
Looking for a Layer 7 attack tool? DDOSSIM is designed to attack the application layer of any service through zombie channels. It contacts and unleashes several zombie hosts and botnets, creating full TCP connections on any server.
- SMTP DDoS
- HTTP DDoS with invalid requests (similar to a DC++ attack)
- TCP connection flood on random port
- HTTP DDoS with valid requests
- Simulates several zombies in attack
- Application-layer DDOS attacks
- Random IP addresses
- TCP-connection-based attacks
For instance, you can create 10 TCP connections from random IP addresses and send invalid HTTP requests to test the server. With just a little practise, this tool can prove to be lethal.
8. R-U-Dead-Yet
RUDY implements generic HTTP DoS attack via long form field submissions. The OWASP group has done a detailed case study and research paper on how this DDoS tool is perfect for testing your system. WIth a user-friendly console menu, you can automatically target any IP or URL.
It supports SOCKS proxies and session persistence using cookies. RUDY or R-U-Dead-Yet should be a handy go-to tool for every system administrator, tester, or developer. It can exploit weaknesses within seconds.
9. OWASP DOS HTTP POST
This OWASP DDoS tool can briefly bring down any system with POST requests. Over the last few years, this tool has been used to test all kinds of networks and servers. OWASP had briefly taken down this DOS testing tool but it is again available for download. You can use it with ease.
OWASP DOS has been developed in Java and is efficient in many kinds of attacks.
- Simulates several zombies in attack
- Application-layer DDOS attacks
- Random IP addresses
- TCP-connection-based attacks
- SMTP DDoS
- HTTP DDoS with invalid requests (similar to a DC++ attack)
- TCP connection flood on random port
- HTTP DDoS with valid requests
10. PyLoris
PyLoris proxies and SSL connections, and can target protocols such as HTTP, FTP, SMTP, IMAP, and Telnet. It is designed to test different kinds of attacks. Attackers usually do not target all the protocols and simply focus on HTTP but it is important that you secure all the points in advance.
It has been seen that DDoS spammers are looking for new ways to get into the system. It is just a matter of time before FTP and IMAP DDoS attacks become common soon.

More about this tool is available here
11. GoldenEye HTTP Denial Of Service Tool
As the name would suggest, GoldenEye is designed to send HTTP requests to the server in order to overwhelm it. It is a handy tool when you just need to work with HTTP attack patterns. Research has shown that attacks originated from China re usually HTTP in nature and this one can help prepare for it.
It is python script HTTP denial of service with HTTP Keep Alive and NoCache features. GoldenEye HTTP Denial Of Service Tool is more popular among the individual testers and college students.
Download GoldenEye easily for free
12. DAVOSET
Introduced in the early 2010, Davoset has been around for a decade now. While it looks like any other tool on the list but this attack tool is unique. It can launch layer 7 DDoS attacks by leveraging other websites and their resources.
It is developed to exploit Abuse of Functionality and XML External Entities vulnerabilities on vulnerable servers. Often attacks launched through this DDoS tool become untraceable and difficult to stop. You can get this tool through GitHub here. Also, there is a full demonstration video depicting the use and functionality of the tool on GitHub link.
Get the tool here
What are the types of DDoS attacks?
Distributed Denial of Service attacks have become a never-ending headache for governments and businesses. Ranging from megabytes to terabytes, you never know what kind of traffic surge will come at what time of the day.
Over the past few years, researchers have identified different kinds of DDoS attacks based on the floods and request types.
Volume Attacks
This kind of attack saturates the bandwidth of the site. Even if you are on a scalable bandwidth, the cost will multiply within seconds. Volume-based attacks are largely used by competitors, ex-employees, and haters to attack sites.
- UDP floods, ICMP floods, and other spoofed-packet floods
Application Layer Attacks
Layer 7 attacks have become increasingly common across the world. SaaS companies often bear the brunt of this type of attacks. The attackers hide botnets and zombies behind usual requests and unleash surges.
- GET/POST floods, low-and-slow attacks, OpenBSD vulnerabilities
Protocol Attacks
If you look at the list of tools above, many of them offer protocols to attack through the interface. This type of attack can eat up resources on your actual server or intermediary services like CDN, load balancer, or firewall.
- Smurf DDoS, fragmented packet attacks, SYN floods, Ping of Death
Here are some of the common attack types:
- UDP Flood
- ICMP (Ping) Flood
- SYN Flood
- Ping of Death
- Slowloris
- NTP Amplification
- HTTP Flood
- Zero-day DDoS Attacks
What is the motivation behind DDoS attacks?
Most DDos attacks are expensive. Using a best DDoS attack tool takes resources, risk and money. Why would someone be interested in wasting their time in harming others? Different kinds of attacks are launched for different reasons. Over the course of 2019 and 2020, researchers have seen an increasing number of shorter duration but high impact DDoS attacks.
Some of the common reasons for DDoS attacks are:
- Competition
Business rivalry is one of the leading causes for this. If a rival online shop has a sale day, the best way to ruin it is through the DDoS surge. It is best to prepare for such instances.
- Cyber Warfare
It is no secret that countries today fight on the cyber front too. States have enough money to fund such misendeavours and there is no shortage of motivation either. With just a few thousand dollars, they can bring down most government sites within hours.
- Money
There are many businesses that are ready to pay ransom to get rid of such attacks. Just like ransomware encrypts the data, DDoS attack tools make it impossible to run business smoothly. Hackers launch long duration attacks after discovering vulnerabilities and demand money to shut them down.
- Fun
College students, hacking enthusiasts, and black hat community often show off their skills through such attacks. There are plenty of underground competitions of such kind. They perform large-scale DDoS attacks just for the fun of it.
- Disagreement
From religious disagreements to ideological differences, there are dozens of other reasons to target certain websites. Today, even social media feuds can trigger such large-scale, global DDos attacks for fun.
DDoS Mitigation
In this piece, we have discussed the major components of DDoS attacks, their types, and different types of tools that you should consider. Cybersecurity and hacking are changing in many ways. A few years ago, you needed sophisticated software and coding knowledge to bring websites down.
However, times have changed. Anyone can launch DDoS attacks with as little as a couple of hundred dollars. Businesses should consider testing and mitigation tools to ensure that their most critical web resources do not go down in the most important days.
When it comes to Security then you need to be very punctual about the safety of your system. You can not say that you are safe by only comparing with old measurements/resources which make your system safe. Hacking enthusiasts are always up to finding new ways to crack the security and enter the system. To really get the idea of what exactly to do next, instead of following old security tips, you need to actually know the process so you can better determine and apply desired changes.
If you are familiar with the term website hacking then you probably know that term DDOS. And this is one of that kind of attack seen usually on the internet nowadays. And we are about to tell you how to DDoS but before you need to clearly know what this is about:
What is DDoS?
DDoS, which is stands for Distributed Denial Of Service and has a huge effect on the internet and its users. It is simply focused on overwhelming the server or system by using various methods to shut down the system. When talking about websites then attacker makes a huge network or bots to send a request to your site server to the maximum of its capacity so the legit users can’t access the site. A DDoS attack can crash the whole site badly. It can be a type of blitzkrieg, DNS server amplification or other types. The force to shut down the system/server or keep it busy as much as possible to prevent the real users to access can be done in more than one manner. And it totally depends on server capacity for how much requests you need to send a single time to make this happen. Usually, a shared server crash easily whereas to perform an attack on VPS or dedicated server is way too difficult and you really need a superbly broad network or bots and environment to make this happen.
To Perform DDoS attack you need to go through these simple steps. We will give you a brief idea on how to DDoS a server. Let’s take a look at below steps explanation:
As we already said that this attack can be performed in various manners, you can also use a different method but here we are running this process using a software as well as the command prompt. Using a software to perform this kind of attack is easy because non-techky or tech knowledgeable person can even use a software after following instructions and can get started right away anytime.
Step 1# Starting the Software
To get started with a software to perform DDoS you need to install one of the best ones which will actually work. Download this software from Sourceforge.net, this software is known as LOIC(Low Orbit Ion Cannon). After one downloading the software, you need to extract it on your windows system and open it.
Step 2# Target A Site
After opening LOIC on your windows system you need to Target a website in which you want to perform this action. Here you will see Select your target box area inside which you have two other boxes contains options to put the Website URL and IP address. If you have the website URL which you want to target then put it inside the first box, Or if you have the IP then put that in the second box. After that hit the “Lock on” button.
Step# 3 Configure it
Be patient and don’t move your fingers towards the big button because still you need to configure and let the software know the configuration of your attack. Now, go to the third section says Attack options, let the Timeout and HTTP Subsite same but inside TCP / UDP message box type any Random message.
Also let the port same (80) if you are attacking a website, then select the method UDP. Uncheck wait for reply and let the Threads at 10. Usually, the Thread should be 10 but if you have pretty good processor/configuration then you can increase it upto 20 which will increase the capability of your attack.
Step# 4 Final Step (Attack)
Now its the time to press the trigger, you see that big button which says IMMA CHARGIN MAH LAZER so hit that. Once you have pressed that you will see the regarding info and the progress of your attack. On request column, under Attack status, you will see how many times the resources of the site has been requested. Or if you are doing ddos on Minecraft server then it will show you for how many times it has requested the resource from Minecraft server.
Ddos Tool
This is just an automated DDoS attack which will work with LOIC and the info you will feed inside of it. If you want to do it manually then you can use command prompt for this purpose. Check out below steps to know exactly how to do this.
How to DDoS Using Command Prompt
In a manual way, you can use cmd for DDoS. It increases the simplicity of task and makes it more convenient. With command prompt, all you need is an enabled Internet connection.
Selecting a site: The First and initial step is to select your target, so choose a site which you wanted to ddos.
Getting IP: In order to DDoS that site you need to get the IP address of that website. Open command prompt and run this command
It will show you the IP address which looks similar to xxx.xxx.xxx.xxx , once you get the IP address press Ctrl+c to stop the current command execution.
Execute DDoS: You need to type the following command to DDoS website.
This command will send the 65500 bytes of data to the ip address or to the site. To make ddos attack more powerful you can use multiple systems and run the command.
Ddos Tool Apk
Stay Tuned: You need to let the command execute for atleast 2-3hours. It will overwhelm the server and the site will go down temporarily.
Note: This attack using command only works with low config server, like shared servers. If you are trying to DDoS a website which has VPS, dedicated or high configuration server then only the tools like LOIC or other powerful tools. will work for you.